The dark web, a shadowy realm veiled in secrecy and anonymity, bustles with illicit activities and hidden knowledge. Accessing this clandestine world requires specialized tools like onion links, gateways to sites constructed using the Tor protocol. OnionLinks serve as the entrances to these hidden servers, offering a devious path through layers of encryption. Navigating this labyrinthine landscape requires awareness, as malicious actors hide within its depths, seeking to prey upon unsuspecting users.
- Understanding the nature of OnionLinks is paramount for users venturing into this virtual underworld.
- Equipped with knowledge and strategy, users can traverse the dark web's complexities with a higher degree of security.
Keep this in thought that the dark web is a double-edged sword, offering both opportunity and threat. Tread carefully, for the path ahead holds perils.
Explore into Onion Links: A Guide to Unlocking the Hidden World
Onion links reveal a shadowy sphere on the web. These links often hide content from casual users, requiring dedication to traverse their enigmatic depths. For the intrepid explorer, onion links yield a peek into a parallel world laden with secrets.
- Exposing the purpose of onion links requires a variety of techniques
- From dedicated software to understanding complex systems, the quest calls for a unique amount of knowledge
- Be aware that the realm behind onion links can be equally fascinating and risky.
Venture with prudence, always prioritizing your safety.
Exploring the Anonymity of Onion Links: Risks and Rewards
The hidden web, a realm accessed via onion links, presents a unique arena of anonymity. While this obscurity offers potential benefits for those seeking privacy or to avoid censorship, it also harbors significant risks. Users diving into this digital netherworld must diligently weigh the potential rewards against the likelihood of discovery.
onionlinks- Abusing this anonymity for unethical activities is a serious concern, as law enforcement agencies struggle in investigating cybercrime within the encrypted environment.
- Moreover, users themselves stay vulnerable to fraud, as criminals can leverage the lack of regulation to defraud unsuspecting individuals.
Breaking the Cipher: Understanding Onion Link Structure
Navigating the labyrinthine world of cybersecurity often involves deciphering complex systems. Among these, onion link structure presents a unique challenge and opportunity. This intricate network, built on layers of privacy, conceals the true destination until the final layer is reached. Visualize a series of nested passageways, each one requiring a specific key to unlock. The onion link structure operates in a similar manner, with each hop hiding the next until you arrive at your ultimate destination.
- Comprehending this layered strategy is crucial for both malicious actors seeking to exploit vulnerabilities and defenders striving to protect against them.
- Analyzing the onion link structure allows us to locate potential weaknesses, mitigate risks, and ultimately create a more secure online environment.
Exploring the Surface: Unveiling Secrets Through Onion Links
The complex world of onion links provides a unique opportunity to uncover hidden information. These concealed pathways guide users into the online realm, that they can investigate a treasure trove of unclassified data. With each click, users journey through various stages, eventually accessing the center of the enigma. Onion links function as a powerful tool for investigators seeking truth. Nevertheless, it is crucial to interact these paths with caution as they sometimes lead users into unforeseen territory.
The Power and Peril of Onion Links: A Digital Double-Edged Sword
Onion links, with their multi-layered structure, can be both a beacon of accessibility and a shadowy gateway to harm. On one hand, they offer anonymity for citizens seeking to engage in sensitive communications. On the other hand, this same layer system can be exploited by malicious actors to evade detection with impunity. The power of onion links is undeniable, but so are the perils they present.
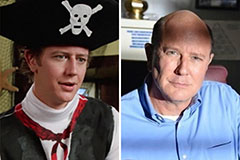 Judge Reinhold Then & Now!
Judge Reinhold Then & Now! Keshia Knight Pulliam Then & Now!
Keshia Knight Pulliam Then & Now! Loni Anderson Then & Now!
Loni Anderson Then & Now! Suri Cruise Then & Now!
Suri Cruise Then & Now! Traci Lords Then & Now!
Traci Lords Then & Now!